Authors:
James F. Kurose, Keith W. Ross
Chapter:
Transport Layer
Exercise:
Problems
Question:9 | ISBN:9780132856201 | Edition: 6
 Question
Question
Give a trace of the operation of protocol rdt3.0 when data packets and acknowledgment packets are garbled. Your trace should be similar to that used in Figure 3.16.
 Answer
Answer
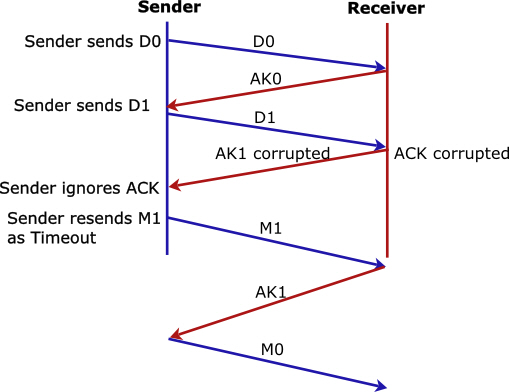
The following figures illustrates the tracing of the rdt3.0 protocol when data packets or the acknowledge (ACK) packets are corrupted.
The sender’s state is “wait for call from above” and the receiver’s state is “wait for 0 from below”.
Figure illustrating data sent by the sender is corrupted:
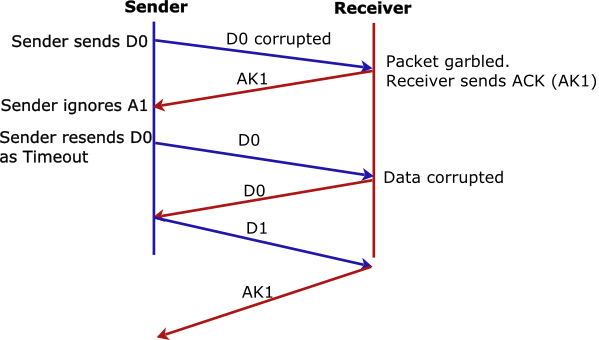
Figure illustrating ACK sent by the receiver is corrupted: