Question
Question
Suppose Alice wants to visit the Web site activist.com using a TOR-like service. This service uses two non-colluding proxy servers, Proxy1 and Proxy2. Alice first obtains the certificates (each containing a public key) for Proxy1 and Proxy2 from some central server. Denote K+1( ), K+2( ), K1– ( ), and K2–( ) for the encryption/decryption with public and private RSA keys.
a. Using a timing diagram, provide a protocol (as simple as possible) that enables Alice to establish a shared session key S 1 with Proxy1. Denote S 1 (m) for encryption/decryption of data m with the shared key S 1 .
b. Using atiming diagram, provide a protocol (as simple as possible) that allows Alice to establish a shared session key S 2 with Proxy2 without revealing her IP address to Proxy2.
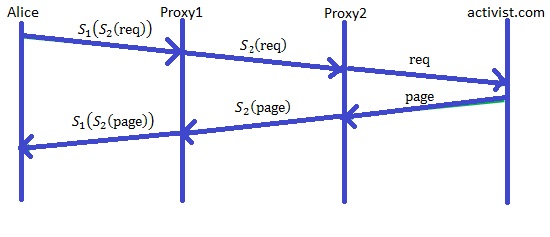
c. Assume now that shared keys S1 and S 2 are now established. Using a tim- ing diagram, provide a protocol (as simple as possible and not using public-key cryptography) that allows Alice to request an html page from activist.com without revealing her IP address to Proxy2 and without revealing to Proxy1 which site she is visiting. Your diagram should end with an HTTP request arriving at activist.com.
 Answer
Answer
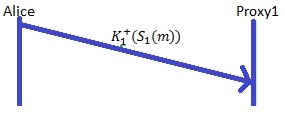
a)
Assume the Alice wants to visit the Web site activist.com using a TOR(The Onion Router) -like service. Take servers Proxy1 and Proxy2.
Alice first obtains the certificates (each containing a public key) for Proxy1 and Proxy2 from some central server.
Designate K+1( ), K+2( ), K1– ( ), and K2–( ) for the encryption/decryption with public and private RSA keys.
The following timing diagram is indicates a session key S1 with Proxy1. Alice encrypts the session key with public key of Proxy1 and sends it to Proxy1. Here S 1 (m) represents encryption/decryption of data m with the shared key S 1 .
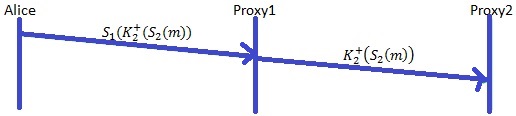
b)
The following timing diagram indicates a protocol (as simple as possible) that allows Alice to establish a shared session key S 2 with Proxy2 without revealing her IP address to Proxy2.
c)
The following timing diagram indicates the a protocol (as simple as possible and not using public-key cryptography) that shows Alice to request an html page from activist.com without revealing her IP address to Proxy2 and without revealing to Proxy1 which site she is visiting. Your diagram should end with an HTTP request arriving at activist.com.